Despite the fact that each of us uses the services of providers and has access to the Internet every day, many things and definitions remain, so to speak, behind the scenes, beyond our sight and understanding.
However, many things need to be known as they are useful and important to everyday Internet users. In this article we will talk about proxy server, its features and capabilities, and understand how a proxy differs from a VPN service and when it is better to use it for anonymity purposes.
What is a Proxy Server
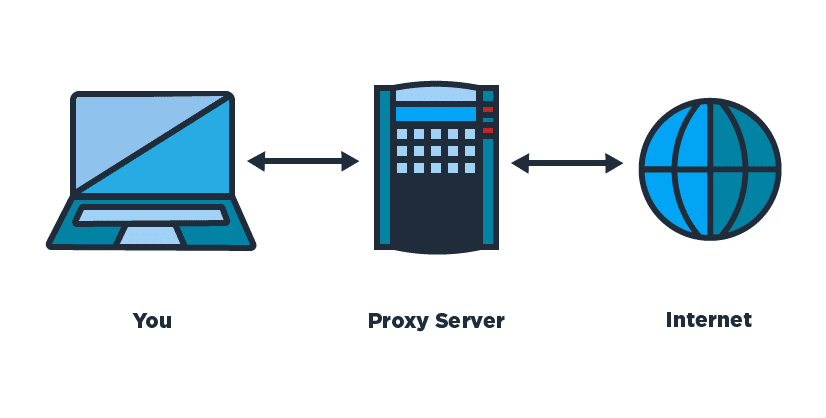
A proxy server is an intermediate server that combines the work of a personal computer and any website, as well as a web resource. If you enter a search engine query from your PC, then before opening a site on the Internet, the query is received by the proxy, then processed and further transmitted to the appropriate web server. The answer from the site will go first to the proxy, and from it – to your computer.
And then the question immediately arises: why so complicate the connection system and use an intermediary link? The answer to this question is their several key features of the proxy itself:
- access to some sites is accelerated;
- access to the Internet through this server is protected by anonymity;
- if you are banned from a resource, you can trickyly bypass censorship and visit the target site, forum, community;
- you can manage traffic on corporate networks.
So, an online proxy server can be described as a remote intermediary to help users access the global network. In this case, the proxy assumes the task of translating all user requests on the Internet and sending him the received responses from sites.
Proxy Varieties
There are several types of proxies:
- FTP – such server is used for data upload;
- CGI is an anonymizer that helps you open any site directly in your browser without any additional settings;
- SMTP, POP3 and IMAP – these are used to send and receive e-mails through mail;
- HTTP and HTTPS – are responsible for browsing the Internet.
The HTTP proxy is considered the most common type and is responsible for organizing the work of browsers, programs using the TCP protocol.
The principle of his work is as follows:
- the proxy receives a request from the browser or program to open a specific resource;
- the server receives data from the site as a response to the incoming request;
- your browser receives a response from the proxy to the target resource.
The HTTP proxy has such features:
- caching of all uploaded files to increase the speed of website opening;
- restricting access to certain web resources;
- data filter, which is relevant for advertising banners, instead of which transparent images are shown, so they do not disturb the design of the site and save download time and traffic;
connection speed restriction; - logging, traffic control for each user.
If we talk about the aspect of anonymity, HTTP proxies can be like this:
- transparent – notification about proxy usage, transmission of real IP-address from the user. This type of connection does not possess anonymity;
- anonymous proxies – a notification about the use of a proxy, the real IP address is not transmitted. There is no 100% anonymity here, because the network receives information about the fact of proxy usage;
- elite – no notification and no real IP address is transferred. Ensure complete anonymity and security.
HTTPS Proxy is a secure version of the previous version and supports SSL connection. This type of proxy is used when transmitting sensitive information, such as logins, passwords, and plastic card numbers.
The principle of HTTPS operation is as follows:
- the proxy connects to the resource, all traffic is encrypted;
- outsiders cannot know what information is being transmitted;
- data is encrypted using the browser and the target server, the proxy is not involved in this;
- acts as a passive intermediary and translator for encrypted data.
The HTTPS proxy is convenient to use for any TCP protocol transmission.
It is worth telling about Socks-Proxy, which is now considered the most progressive protocol for information transmission. Originally it was developed for programs which did not support proxies.
Now two versions of it are actual:
- Socks-4 – support only for TCP-connections;
- Socks-5 – support for TCP, UDP, authorization by login and password, remote DNS-request.
Socks-server always transmits information through itself in pure form, which already indicates its complete anonymity. However, the real IP is not broadcast, also the site can not determine the fact of proxy use. Connection to any web resource is transparent and the site sees the IP of the proxy server, not your own.
How Does a Proxy Server Work
Since a proxy is a program that manages requests between a user and the end web resource, it can be installed on a PC or server:
the proxy gets to the user’s PC through Trojans or viruses. In this case, it will fulfill all your requests and provide complete anonymity, but you do not receive any guarantee of stable and continuous operation;
the proxy server online is considered the most reliable and stable. But you do not receive any guarantee of anonymity, because it is known who owns the server.
Paid proxies are reliable programs with a high level of anonymity.
Free proxies can be found on specialized sites, but consider that in this case there will be no anonymity of surfing on the Internet.
Appearances of free proxies are caused by the following reasons:
- incorrect access settings by the local network administrator;
- universities and educational institutions may access local libraries through proxies;
- proxies from government agencies.
It is not recommended to use free proxy servers, as it is dangerous. Sometimes public services specifically place their proxies to keep track of those who use them.
The main feature of the proxy server is to accelerate the work of sites and surfing the user on the Internet. This is due to two key factors:
- the proxy server is located close to you compared to the target sites;
- the proxy has a powerful communication channel.
Work in the global network is accelerating because..:
- a high data rate is set between the user’s PC and the proxy;
- the connection speed to the sites is known to be higher;
- caches information that can be used not only by you, but also by other users, i.e. the cache is shared by all;
- through one proxy you can connect to another, then to the next, and so the whole chain is built.
How to Set Up a Proxy Server
The instructions on how to install and configure a proxy server on windows 10 are as follows:
- download and install the Putty utility, on the Session tab write the IP address specified in the letter when creating the VPS;
- Tunnels tab – SSH section;
- enter the number 3128 on the Source Port line;
- select Auto and Dynamic values – click Add;
- Connection tab – set the time to 100 seconds, then the connection will not be broken;
- the Open button to make the connection;
- enter the login and password that you received from the host after creating the VPS.
Below we will consider an example of proxy server configuration in Google Chrome browser.
The first step is to clear the cookies:
- Google Chrome Settings – to get more settings;
- Personal data section – Clear history – select the period for all time;
- select Clear cookies and other data from websites and plug-ins – select the Clear history button.
To configure a proxy, you need to follow these steps:
- Google Chrome settings – call up additional settings;
- System section – proxy server settings;
- local network settings field – click the Network Setup button – check the Automatically detect and Use for local connections box;
- click Advanced – SOCKS line – specify localhost address and port 3128;
- check the IP address of your computer to see if the poxy server connects to sites.
If you are working with another browser, the setting will be similar. You can also set up a free online proxy server in your smartphone or tablet regardless of your operating system.
If you want to disable the proxy, you need to clear the Use proxy server for local connections check box in your local network settings.
The Difference Between Proxy and VPN
The VPN service is used to hide an IP address and create anonymity for the user while surfing the Internet. In fact, Proxy does the same, but there are significant differences between the two programs due to the way each connection works.
If we consider both proxy and vpn services in relation to the IP hiding function, then the difference appears at the OSI (network data model) level. The proxy server performs its task at the application layer, and the VPN – at the network or channel level. In other words, completely different technologies are used.
The role of vpn proxy can be any server that can perform user requests on its behalf. In most cases, it works using only one protocol.
Although the exceptions are HTTPS and SOCKS5, which tunnel any TCP connection.
A proxy server cannot be adapted for all programs because everyone must know that the connection is made through a proxy.
With regard to VPNs, this is a virtual private network that generates a connection for programs in the form of a network adapter. Any program can work through the VPN without even knowing it exists.
Conclusion
A proxy server can be a good alternative for VPN if you want to be anonymous on the network. However, these technologies are not identical, and the proxy has its own features. Of course, you will leave a trail on the Internet, but with the paid version of the program you can completely hide, it’s up to you to decide whether you need such a server, whether you want to go deep into what a proxy is, or whether you can surf the network openly and let hackers hack into your data.